
Making e-mail secure and dealing with spam
Electronic mail is one of the most used forms of communication. It is heavily abused by spammers and hackers, it is usually totally insecure, assures no privacy (i.e. does not encrypt message contents and information resting on servers), no message integrity (that contents have not changed in transit), does not authenticate e-mail senders (users) nor the servers used to send and receive messages.
In order to understand how to protect e-mail you must know which part must to be handled on the "server" side (by your e-mail provider) and what part must be handled by the you (the e-mail user that wishes to send and receive messages).
E-mail servers/providers
The e-mail transport/format is based primarily on very old and outdated protocols like (E)SMTP (latest revision in 1995), POP3 (latest revision in 1993) and IMAP (lastest revision in 2003).
Some complementary protocols help by creating an association between DNS records of the domain servers that are allowed to send email from that particular domain. SPF, DKIM and DMARC are the most widely used and are really important as far as fighting SPAM.
Every single e-mail should be protected with either SPF (minimum protection), DKIM (slightly better protection) or DMARC (best commonly used). You can personally test your current provider easily (and it is something you should do).
SPF
You can use any of the web on-line testers like https://www.dmarcanalyzer.com/spf/checker/
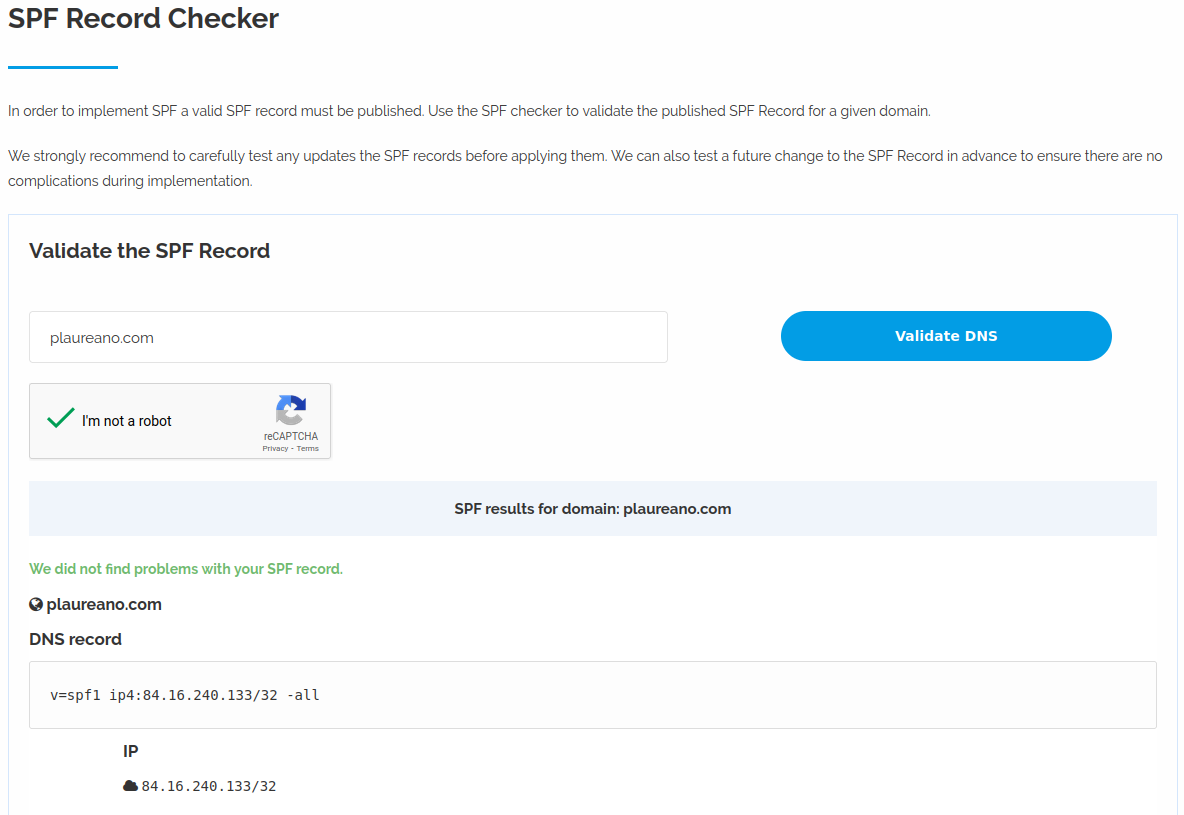
You should see something like what appears on the above message. Pay special attention to the last part of the returned content: if you see "~all" it means that messages that come from rogue servers should be treated as potential spam, if you see "-all" it means that they should be immediately discarded/refused and never shown to users at all.
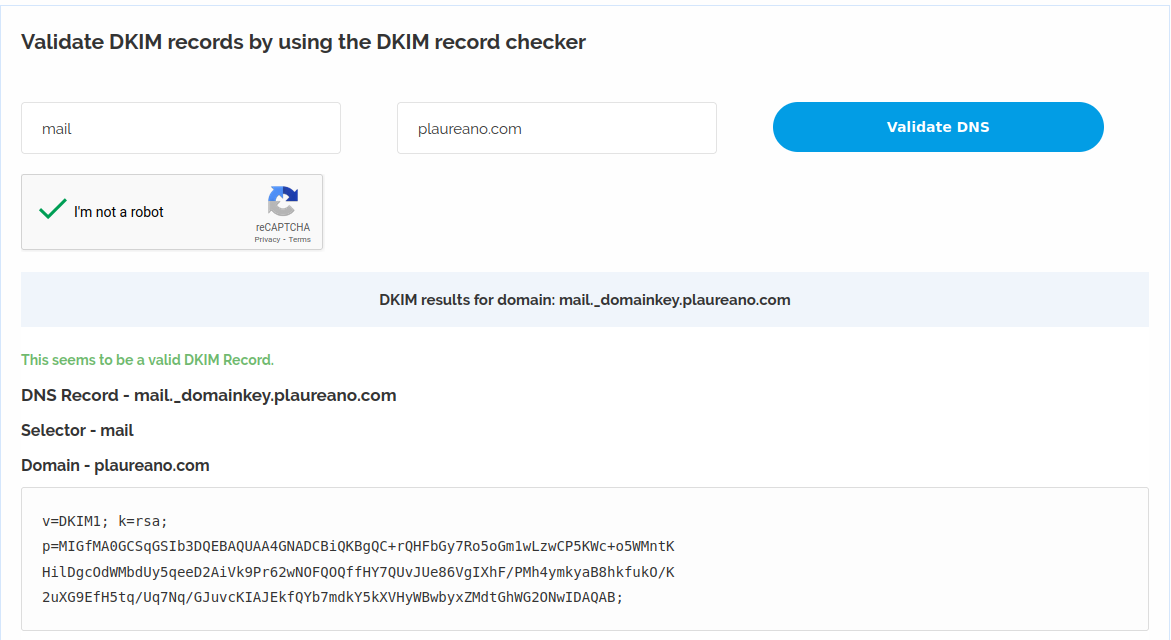
DKIM
You can use any of the web on-line testers like https://www.dmarcanalyzer.com/dkim/dkim-checker/
DMARC
You can use any of the web on-line testers like https://easydmarc.com/tools/dmarc-lookup
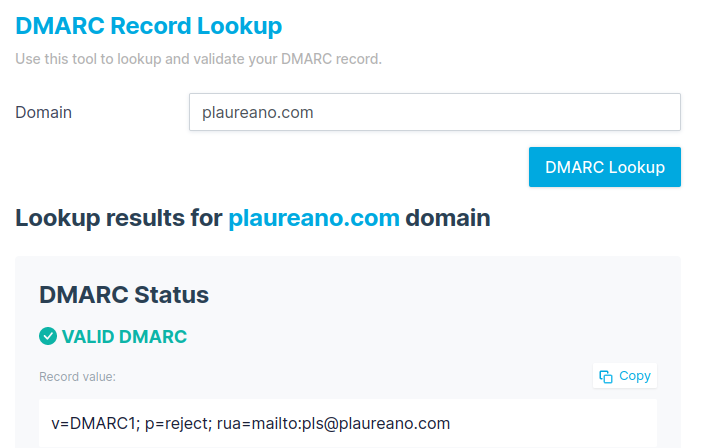
Pay special attention to the "p=" field in the results. "reject" means mail from rogue servers should be discarded/refused and never reach the recipient. Other values in the policy record mean that it is up to the mail service providers anti-spam tools to decide what to do with the message. These tools can either do a good job (i.e. not accept and not deliver the message) or nothing at all. You can know for sure your mail provider is doing to protect you by sending a test message that should never reach your inbox at https://dmarc-tester.com/
Individual E-mail users (and companies e-mail clients)
The identity of the message sender (that it really comes from that particular individual or company) and the integrity of message content (i.e. has not been modified in transit) can be ensured by S/MIME certificates and GPG/PGP.
S/MIME
You can read all about which e-mail clients support S/MIME here: https://www.rapidsslonline.com/ssl/what-is-s-mime-email-certificates/
The only FREE provider I know of (and use) of S/MIME certificates (for personal use) is https://www.actalis.com/s-mime-certificates.aspx
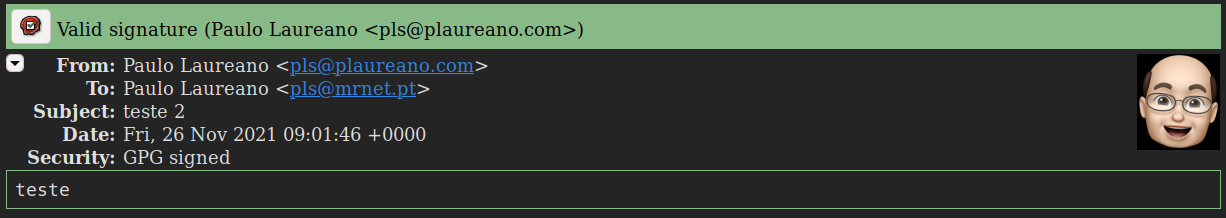
GPG/PGP
Most e-mail clients support GPG/PGP: https://www.openpgp.org/software/
OpenGPG is free to use on every platform known to mankind.
What do you see when you receive a signed message?
It depends on your e-mail client, but usually you see some symbol telling you that the message is digitally signed (or encrypted) by either S/MIME or PGP/GPG.
I get it, most users will never get to protect themselves and others. Most people can barely send or receive e-mails. But the more capable among you should put some effort into making e-mail safer for everyone.
Companies that e-mail individuals should always sign their messages. There is no good excuse whatsoever to place your clients in danger and leave them susceptible to fake e-mails sent in your name. You, as a customer, should demand it from companies that interact you you by e-mail. This is especially true for banks and e-commerce stores that e-mail you financial information and documents (like invoices and receipts). Start educating companies that interact with you!
This article was published on Medium (I am a subscriber and highly recommend it).



